The modern extortion cycle targeting international students—specifically the Chinese diaspora—operates not as a series of random crimes, but as a sophisticated cross-border service delivery model. This model exploits the friction between high-trust cultural backgrounds and the opaque regulatory environments of host nations. By weaponizing the "State Authority Proxy," criminal syndicates induce a psychological state of total compliance, converting a student’s legal status into a liquidatable asset. To dismantle these operations, one must understand the three specific vectors of attack: jurisdictional confusion, the social proof of physical gold, and the systemic isolation of the victim.
The Triad of Psychological Leverage
The success of these money-laundering "investigations" rests on a foundation of manufactured urgency. The attacker does not merely lie; they build a comprehensive, simulated reality that the victim cannot easily exit.
1. The Jurisdictional Black Hole
International students exist in a state of legal precariousness. Their right to remain in a host country (the UK, Australia, or Canada) is contingent upon maintaining a "clean" record. Scammers exploit this by claiming the student’s identity has been used in a money-laundering scheme in their home country. Because the victim cannot easily verify the claims with domestic police due to geographical and political barriers, the scammer occupies the role of the "sole arbiter of truth."
2. The Authority Proxy
The operation begins with a "transfer" of the call from a low-level official to a high-ranking "prosecutor" or "investigator." This uses the Principle of Escalation. By moving the victim through a hierarchy, the scammers mirror the actual bureaucratic experience of dealing with a government entity. They provide fake warrant IDs, official-looking documents via encrypted apps like Telegram or WeChat, and strict "secrecy orders."
3. The Isolation Protocol
The most critical phase is the enforcement of total silence. Victims are told that any communication with friends, family, or local police will result in immediate arrest for "leaking state secrets." This creates a closed loop where the only feedback the victim receives is from the predator.
The Physical Liquidation Pivot: Why Gold?
A recent and alarming shift in these probes involves the demand for physical gold rather than traditional bank transfers. This is a tactical adjustment to the tightening of Anti-Money Laundering (AML) and Counter-Terrorism Financing (CTF) protocols within the global banking system.
When a victim attempts to transfer $50,000 to an offshore account, modern banking algorithms flag the transaction for "unusual activity." Physical gold provides several advantages to the criminal enterprise:
- Bypassing Digital Friction: Gold purchases at retail bullion dealers often fly under the radar of automated fraud detection systems, especially if the victim uses multiple smaller transactions.
- Irreversibility: Unlike a wire transfer, which might be clawed back or frozen within the first 24 to 48 hours, a physical hand-off of gold is a final settlement.
- Anonymity of Transport: Once the gold is collected—often by a "courier" or via a secure drop-off point—it is nearly impossible to track through the digital financial system.
- Value Density: High-carat gold allows for the movement of significant wealth in a small, easily concealed physical form.
This "Physical Pivot" reveals a sophisticated understanding of the Cost Function of Laundering. As digital tracking becomes more expensive for criminals (due to the risk of account freezes), moving to a physical medium reduces their operational risk, even if it adds the logistical complexity of a physical pickup.
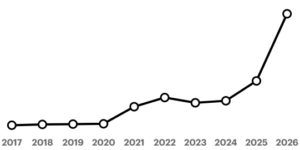
The Lifecycle of a Money Laundering Probe Scam
The operation follows a rigorous linear progression that can be mapped to a standard sales funnel, albeit with a coercive end goal.
Phase I: Prospecting and Data Acquisition
The initial contact is rarely random. Data breaches from educational consultancies, visa processing agencies, or international shipping companies provide the "leads." The scammer knows the victim’s name, their home city, and often their passport details, which provides immediate, unearned credibility.
Phase II: The Hook (The Accusation)
The caller impersonates a logistics company (claiming a package containing illegal documents was intercepted) or a government agency. The goal is to move the victim from a state of calm to a state of High-Arousal Fear. In this state, the prefrontal cortex—responsible for critical thinking—is bypassed in favor of the amygdala’s "fight or flight" response.
Phase III: The Audit (Asset Mapping)
Once the victim is hooked, the "prosecutor" requires a full financial disclosure to "verify the source of funds." The victim is instructed to list every bank account, savings balance, and asset. This is a cold, clinical inventory-taking process that allows the scammer to calculate the maximum extraction value.
Phase IV: The Extraction (The "Bail" Payment)
The scammer presents a solution: the victim must move their funds to a "government-controlled safe account" or purchase gold for "forensic testing" to prove the money isn't tainted by crime. The victim is told the assets will be returned once the investigation concludes.
Structural Vulnerabilities in the Student Ecosystem
Why do these scams continue to yield high success rates despite public awareness campaigns? The answer lies in the Incentive Misalignment between the student and the host institutions.
- Fear of Local Authorities: Many international students come from cultures where the police are seen as an arm of the state rather than a protective service. They fear that reporting a "home country investigation" to local police will result in their deportation by the host country.
- Lack of Financial Literacy in Host Markets: Students often do not understand that Western police forces do not conduct "digital audits" via WeChat or ask for bail payments in the form of bullion or gift cards.
- The Digital Enclave: International students often live within a digital bubble—using home-country social media and messaging apps. Local law enforcement and university alerts often fail to penetrate these enclaves, leaving the students in an information vacuum.
The Failure of Current Mitigation Strategies
Current advice—"just hang up" or "be aware"—is insufficient because it treats the symptom rather than the systemic cause. Universities and banks operate on a Reactive Model, issuing warnings after a spike in cases. A Proactive Model requires a shift in how international student services are delivered.
- The Verified Communication Bottleneck: There is no centralized, multi-language verification system where a student can check the validity of a "government" claim.
- The Reporting Paradox: To stop the scam, the student must trust a system (the host police) that they have been conditioned to fear by the scammer.
Strategic Counter-Measures for Institutional Stakeholders
To neutralize this threat, universities and financial institutions must implement a "Defense in Depth" strategy that targets the scammer's operational requirements.
1. Inter-Jurisdictional Verification Protocols
Universities must establish direct lines of communication with embassy attachés. A "Single Source of Truth" portal should be created where students can submit the details of a purported investigation to be verified by actual consulate staff within 24 hours.
2. Financial Circuit Breakers
Banks should implement a "Cooling Off" period for large-value gold purchases or transfers by student-visa holders to unknown offshore accounts. This is not a restriction of liberty, but a friction-based defense designed to break the "Manufactured Urgency" of the scammer.
3. Peer-to-Peer Resilience Networks
The most effective defense is a social one. Scammers rely on isolation. Creating peer-led "Incident Response" teams within student unions—where students can discuss suspicious calls in their native language without fear of institutional reprisal—destroys the "Isolation Protocol."
4. Decoupling Visa Status from Criminal Inquiries
Host governments must provide a "Safe Harbor" declaration, explicitly stating that being the subject of a foreign inquiry—or being a victim of a scam—will not automatically trigger a visa review. Removing the fear of deportation removes the scammer's most powerful weapon.
The objective is to increase the Cost of Victim Acquisition until the business model becomes unviable. As long as the extraction of $100,000 in gold remains easier and safer for the syndicate than traditional cybercrime, the student diaspora will remain the primary target. The intervention must be structural, moving beyond "awareness" and into the realm of active friction and jurisdictional clarity.